I was thinking a bit about the bugs I found in the Piefed codebase yesterday. And these led to an emergency fix by the dev that’s now been implemented. https://codeberg.org/rimu/pyfedi/commit/093a466935849f27b3ecf2eab159129186320417
And what the real takeaway for me here is that the whole dynamic of how we approach security has now changed in ways most people don’t appreciate.
It used to take a lot of effort to find exploits in software projects because you’d have to spend a long time to familiarize yourself with the codebase, then comb through the code looking for mistakes that could be exploited. And to even do that, you’d need a good understanding of the protocols and specifications used by the application.
You basically had to be a domain expert with a deep understanding of how the application works. A random person looking at the source code would have little chance of finding any non trivial problems or figuring out how to actually exploit them.
And in that world, doing a private disclosure made a lot of sense because you did a lot of hard work to find it, and it wasn’t easy for somebody to replicate. This was valuable and dangerous knowledge that had to be communicated in a responsible fashion.
But now, anybody can throw an LLM at the code and it’ll sniff out vulnerabilities and even explain step by step how to exploit these security holes. So, the information itself isn’t really that valuable anymore. If I can throw an LLM at the code and find these problems in a few minutes, anybody else can do the same thing too.
I’m not a Python developer, I don’t have any deep knowledge of the Python stack used in Piefed, and on my own, I’d have zero chance of finding these exploits. But once the LLM identifies them, it’s very easy for me to verify that they are indeed real exploits, and to realize how they can be used maliciously.
The attacker doesn’t even need to have any deep knowledge of programming because the LLM can guide them through the exploit step by step.
Open source projects are particularly vulnerable here since anybody can just grab the source and throw an LLM at it to see if it can find exploits.
I’d argue that raising awareness that this is now the state of things is really important, and I would suggest that running an LLM against the code is minimal due diligence at this point.
Obviously, the LLM vulnerability check is not exhaustive, and if it doesn’t find anything that doesn’t mean there aren’t exploits in the code. But anything it does find should absolutely be checked by the developers.
People should be aware that we’re now living in the world where the bar for finding vulnerabilities is far lower than it used to be. And that means security must be taken far more seriously.
Responsible disclosure is still important because it takes the developer time to develop, validate and release a securit fix. Keep in mind that open source projects like Piefed, Lemmy and others are developed by volunteers in their free time. So it is irresponsible to publish security problems without any private warning. For all the infighting that is happening, we need to remember that our enemy is Reddit, and not anyone on the Fediverse.
sorry - you used a non-deterministic system to find a bug, and you’re saying there’s no duty to disclose responsibly because someone else could maybe use a similar system to maybe find that bug?
Edit: elsewhere you say this
Since the exploit is very easy to find, it should be assumed that malicious people would have found it as well
While it’s possible that someone else has found it, this is not a reason to hand it to malicious people on a platter.
Wait till you find out that the human brain is also a non-deterministic system.
Exactly - so why is this a bug that should be disclosed publicly
Since it affects people running the software and very likely to be known to any malicious actor I would argue so. I’ll stress again that this was not information that took any effort to find. Literally a few minutes of effort.
It’s also been happening in the Linux kernel with copy fail/dirty frag and the related exploits found once people started looking deeper.
Wild times ahead in good and terrible ways
i cant believe the Feds are blaming you for finding a vulnerability lol, rimu didnt even mentioned you in the post, what a fucking shitshow lol
I continue to be disappointed in blaze as they are going oh it was no big deal AND happened already in lemmy.
truly
And in that world, doing a private disclosure made a lot of sense because you did a lot of hard work to find it, and it wasn’t easy for somebody to replicate. This was valuable and dangerous knowledge that had to be communicated in a responsible fashion.
Private disclosure still makes sense to me when you add LLMs into the mix. It is possible that an LLM outputs some plausible-sounding story that over-estimates the actual risk and impact of the exploit. If this story is publicly announced to people who use the software but are not capable of assessing these risks themselves, this can easily have a negative unnecessary consequence - for example, people may bring their server down until an expert or developer provides an assessment or fix.
This is a source of noise, and I don’t agree that this is better than private disclosure. Via public disclosure one is applying a lot of pressure to the developer(s) to prioritize whatever is being disclosed, which may not always be the nicest thing to do, especially if the impact is not as significant as the LLM suggests. This may not have been what happened in your case (I don’t know the details), but I am thinking about the idea of the average person disclosing publicly LLM-discovered vulnerabilities.
I’m not talking about a scenario of a hypothetical exploit here. I’m talking about a concrete scenario where somebody finds an exploit and verifies it. In that case, people operating the software need to be aware of the vulnerability in the application they are running. Since the exploit is very easy to find, it should be assumed that malicious people would have found it as well.
You’re arguing against a case where you have an unverified exploit that LLM might’ve hallucinated. This is not the case I’m describing. And this provably did not happen in my case as is clearly evidenced by the fix the dev had to make in their server.
Definitely, disclosing (either private or publicly) a vulnerability that has been verified is significantly better than passing on the LLM output without verifying it.
It isn’t my intention to argue one specific case. What I think is that normalizing public disclosure of LLM-inspired vulnerabilities would lead to a wide distribution of cases. We would have some successful cases like yours, and also some cases of the type that I have mentioned. Increase in disclosures will raise the noise floor, and the fact that it is done publicly adds the additional pressure that I mentioned.
I see your point, but I don’t agree that the benefit of public awareness offsets the increase in noise. This disagreement isn’t rooted in aspects that we can objectively quantify though - we just have a difference of opinion here.
It would all depend on the rate of false positives, and as you say, we’d have to wait and see how this plays out. At the very least, what I’d want people to take away from this is that project maintainers absolutely should be using these tools themselves. They’re the people who are in the best position to decide whether something is a real issue, and it’s better to be safe than sorry here.
And what the real takeaway for me here is that the whole dynamic of how we approach security has now changed in ways most people don’t appreciate.
…
now, anybody can throw an LLM at the code and it’ll sniff out vulnerabilities and even explain step by step how to exploit these security holes. So, the information itself isn’t really that valuable anymore. If I can throw an LLM at the code and find these problems in a few minutes, anybody else can do the same thing too.
is this something others agree on as well? Is this how the industry is changing? I don’t know what you mean by “takeaway”, what are you basing this lesson on?
I however still think it irresponsible. Even if it is very easy, the fact that it wasn’t discovered or abused meant no one was looking, but posting it publically made piefed a target. It also meant people didn’t have time to assess and react but everything had to happen now and suddenly and a fix had to be rushed.
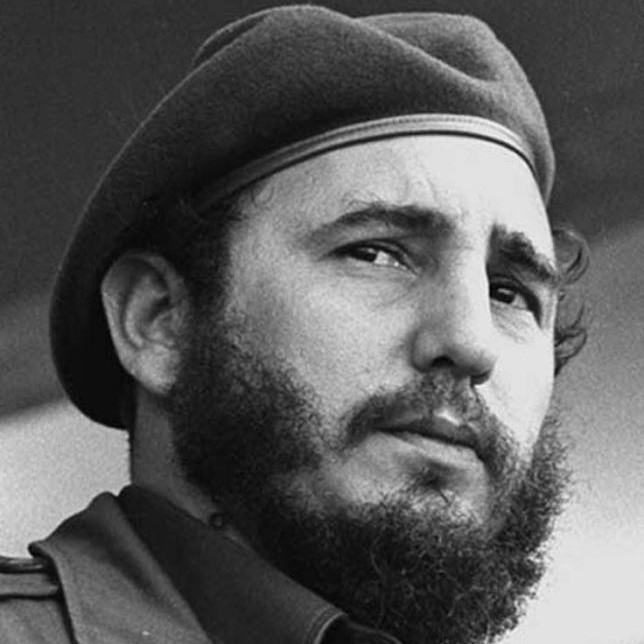
To be blunt, since this comes on the heels of rimu making a huge ass of himself, it looks like (whether true or not i cant know) a dunk on rimu with little consideration to how others might be affected or who was put at risk. Especially to those who don’t know the ins and outs of responsible disclosure practices. And your first response being “If the lead developer was a decent human being, I probably would’ve handled this differently.” kind of makes it hard to shake this feeling.
Yes this whole situation should have been handled in a much more mature manner.
I’m basing this on the demonstration I provided yesterday and the fallout we see from it. Piefed had to go down for maintenance as a result of these vulnerabilities https://lemmy.ml/post/47393443 and I linked to the dev having to apply the fix in the post.
These were real security issues that anybody could find and exploit with very little effort or programming knowledge. We also don’t know that hasn’t been discovered or abused until I surfaced it. If there is a vulnerability that’s trivial to find and exploit, it should very much be assumed that people are doing so.
Rimu being an ass was a contributing factor that motivated me to look at the codebase. But having reflected on it, I stand by my position that raising awareness of the issue and warning people federating with piefed is far more important in this kind of scenario. If this was a difficult to find exploit that nobody would be reasonably expected to have access to in the wild, then the calculus would be to notify the maintainer and let them fix it quietly on their own time. However, when the likelihood is that this is something that people would already be exploiting because the bar for discovering the flaw is so low, warning the public becomes a bigger concern.
your conclusion is definitely correct. the good thing is that if these LLMs can be used offensively to find exploits, they can also be used defensively to find (and potentially even fix) the same ones.
I’m still of the opinion that AI is a tool that amplifies the abilities of the user, so there will be a mismatch of capability depending on that.
with that argument in mind, open source has the potential to be a huge receiver of benefit, if these tools are used to aid development in that way.
overall, what I think that means (what I hope it means) is that we’ll see a much more broad interest in learning secure development as AI research progresses and these tools become more widespread in usage.
I think so as well. These tools work both ways, and a project maintainer is in a much better position to use them effectively than a random attacker by virtue of having a deep understanding of what the code is doing. LLM is just a tool that helps you dig through a huge volumes of information, like a large codebase, and surface things that might be of interest. You still need a human to understand what it surfaces and to take meaningful action.
Hopefully this kind of stuff does get people thinking about security a bit more, and how LLMs can be used to help surface issues.
On my own, I’d have zero chance of finding these exploits. But once the LLM identifies them, it’s very easy for me to verify that they are indeed real exploits, and to realize how they can be used maliciously.
P ≠ NP scores another win.
🤣