I make and sell BusKill laptop kill cords. Monero is accepted.
- 25 Posts
- 9 Comments

 1·1 year ago
1·1 year agoRemoved by mod

 3·1 year ago
3·1 year agoRemoved by mod

 2·1 year ago
2·1 year agoRemoved by mod

 3·1 year ago
3·1 year agoRemoved by mod

 2·1 year ago
2·1 year agoRemoved by mod

 1·1 year ago
1·1 year agoRemoved by mod

 1·1 year ago
1·1 year agoPlease read the question. I am not the developer; I can’t change to keycloak.

 211·2 years ago
211·2 years agoHi, Michael Altfield here. I was the sysadmin for OSE from 2017-2020.
Everything OSE does is transparent, so you can just check the OSE websites to see what everyone is currently working-on. OSE contributors log their hours in a worklog called “OSE Dev”. There you can quickly see who is working on what.
The above graphs show 4 contributors in the past ~10 weeks (one is me; we had some issues with the apache config recently). There’s no direct link, but you can then check the wiki to see people’s work logs (just search for the person’s name and
Log):- https://wiki.opensourceecology.org/wiki/Marcin_Log
- https://wiki.opensourceecology.org/wiki/Catarina_Log
- https://wiki.opensourceecology.org/wiki/Alexa_Log
- https://wiki.opensourceecology.org/wiki/Maltfield_Log
I also like to look at the MediaWiki “Recent Changes” page to peak at what people are up-to as well:
I told Marcin about Lemmy back in June 2023. Another OSE contributor even created an OSE community on the slrpnk.net instance, but it appears to have been abandoned. I’ll email him about this thread to see if he’ll bite and publish updates in this community since there’s clearly interest :)
Also, shameless plug: I started an org that’s very similar in spirit to OSE called Eco-Libre, with a focus on projects to sustainably enfranchise human rights in smaller communities. We’re currently accepting volunteers ;)
You definitely can do that, but if you’re afraid that you might stand-up and forget you’re using it, then you probably shouldn’t.
It’s probably enough to just use the default trigger that locks your screen. Or, once you get comfortable with it, set it to shut down your computer. Most people don’t need to shred their FDE keys, unless they’re facing torture.
In fact, we make it difficult to use “destructive” triggers (like the LUKS Header Shredder that wipes the FDE header) and intentionally do not include the ability to switch to it in the app. To use it, you have to do a lot of extra work. So most users don’t have this issue.
Why? It defaults to just locking your screen. So you stand-up, the magnetic breakaway cable separates, and then you just have to type your password…
If you’re the type of person that would forget to lock your computer before standing up and walking away, then it’s exactly what you’d want.

 22·3 years ago
22·3 years agoIt has a magnetic (de)coupler, which allows it to break away at any angle if your laptop is physically snatched away from you.
Some of our users actually use the BusKill cable with a Yubikey:
If that’s not clear, I highly recommend watching this 2-minute explainer video

 51·3 years ago
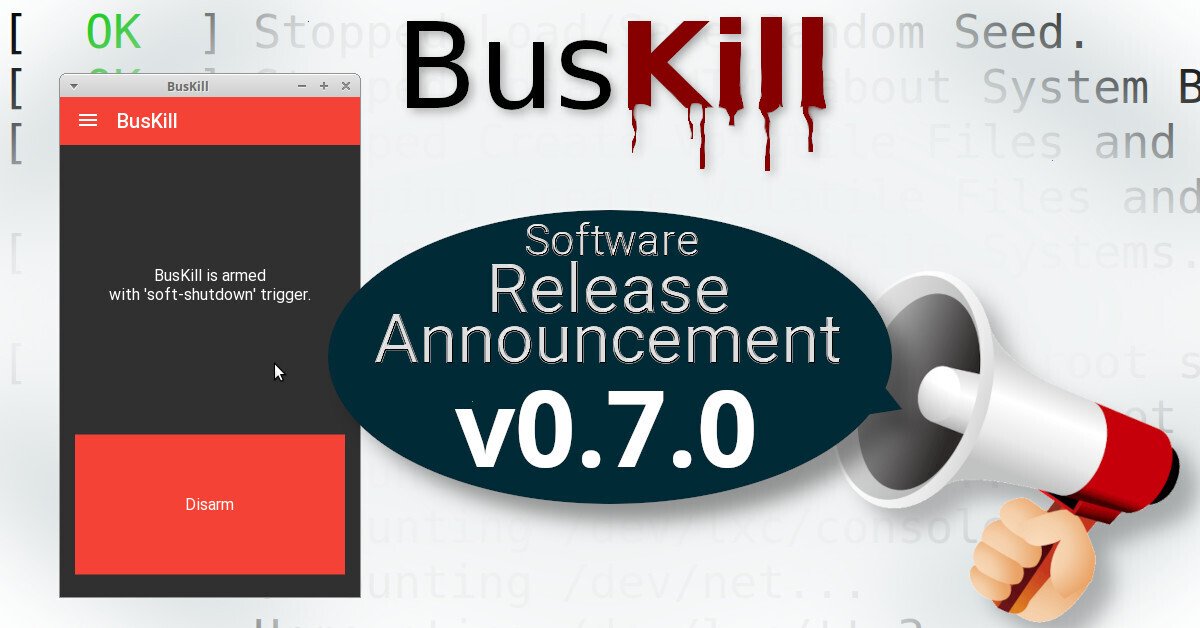
51·3 years agoI build open-source USB Dead Man Switches and the accompanying (also free) software

Watch the BusKill Explainer Video for more info youtube.com/v/qPwyoD_cQR4 You attach the kill cable to your body and if the connection between you to your computer is severed, then your device will lock, shutdown, or shred its encryption keys. It’s designed to protect high-risk users’ data. Data could include private keys (eg theft of cryptocurrency assets), contacts of correspondence (eg sources of a journalist – such as whistleblowers), etc.

 61·3 years ago
61·3 years agoI’ve paid myself nothing so-far. The price just barely breaks-even for the business. There’s one-time costs like a few grand for a CNC’d injection mold and assembly jig, but also certification fees, product boxes, cardstock paper for documentation inserts, printing fees, artist commissions, packaging materials, warehousing, shipping, other logistics fees, etc.
All of this is explained in-detail in “The Finances” section here.
I prefer open-source hardware to be designed using common off-the-shelf items that are easily found everywhere in the world. Unfortunately, the one vendor of a USB-A magnetic breakaway couplers decided to EOL their product shortly after I published a guide on how to build your own BusKill cable. After we published, they all got sold-out, and we had to go to manufacturers for a custom component.
Prices would drop dramatically if we could do production runs (and actually sell) >10,000 units at a time. Currently we only sell a few cables per month. If you want to help, please tell all your security-conscious friends about BusKill :)

 51·3 years ago
51·3 years agoUnfortunately, that’s what it costs to make open-source hardware at small-scale.
There’s a cheaper $59 cable available or you could build your own.

 31·3 years ago
31·3 years agoRemoved by mod

 41·3 years ago
41·3 years agoRemoved by mod

 82·3 years ago
82·3 years agoRemoved by mod
 01·3 years ago
01·3 years agoI’m curious if any security engineers have covered this incident.
Stripe does support generating Restricted API Keys. With “Restricted API Keys” you’re able to mint a key that can live on your e-commerce website that has permission to accept payments but does not have permission to modify your merchant account’s payout methods (eg adding a new “Instant Payments” debit card to the merchant account as this attacker did).
Unfortunately, I’ve asked WooCommerce to support Restricted API Keys 1 year ago, but they marked it as “low priority”
…I would appreciate if more people would jump-in on ^ that ticket and scold WooCommerce so that they add support for Restricted API Keys ;)













Removed by mod